Journal Description
Information
Information
is a scientific, peer-reviewed, open access journal of information science and technology, data, knowledge, and communication, and is published monthly online by MDPI. The International Society for Information Studies (IS4SI) is affiliated with Information and its members receive discounts on the article processing charges.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), Ei Compendex, dblp, and other databases.
- Journal Rank: CiteScore - Q2 (Information Systems)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 18 days after submission; acceptance to publication is undertaken in 2.9 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
Impact Factor:
3.1 (2022);
5-Year Impact Factor:
2.9 (2022)
Latest Articles
Two-Stage Convolutional Neural Network for Classification of Movement Patterns in Tremor Patients
Information 2024, 15(4), 231; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040231 - 18 Apr 2024
Abstract
Accurate tremor classification is crucial for effective patient management and treatment. However, clinical diagnoses are often hindered by misdiagnoses, necessitating the development of robust technical methods. Here, we present a two-stage convolutional neural network (CNN)-based system for classifying physiological tremor, essential tremor (ET),
[...] Read more.
Accurate tremor classification is crucial for effective patient management and treatment. However, clinical diagnoses are often hindered by misdiagnoses, necessitating the development of robust technical methods. Here, we present a two-stage convolutional neural network (CNN)-based system for classifying physiological tremor, essential tremor (ET), and Parkinson’s disease (PD) tremor. Employing acceleration signals from the hands of 408 patients, our system utilizes both medically motivated signal features and (nearly) raw data (by means of spectrograms) as system inputs. Our model employs a hybrid approach of data-based and feature-based methods to leverage the strengths of both while mitigating their weaknesses. By incorporating various data augmentation techniques for model training, we achieved an overall accuracy of 88.12%. This promising approach demonstrates improved accuracy in discriminating between the three tremor types, paving the way for more precise tremor diagnosis and enhanced patient care.
Full article
(This article belongs to the Special Issue Signal Processing and Machine Learning II)
Open AccessArticle
A Novel Dynamic Contextual Feature Fusion Model for Small Object Detection in Satellite Remote-Sensing Images
by
Hongbo Yang and Shi Qiu
Information 2024, 15(4), 230; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040230 - 18 Apr 2024
Abstract
Ground objects in satellite images pose unique challenges due to their low resolution, small pixel size, lack of texture features, and dense distribution. Detecting small objects in satellite remote-sensing images is a difficult task. We propose a new detector focusing on contextual information
[...] Read more.
Ground objects in satellite images pose unique challenges due to their low resolution, small pixel size, lack of texture features, and dense distribution. Detecting small objects in satellite remote-sensing images is a difficult task. We propose a new detector focusing on contextual information and multi-scale feature fusion. Inspired by the notion that surrounding context information can aid in identifying small objects, we propose a lightweight context convolution block based on dilated convolutions and integrate it into the convolutional neural network (CNN). We integrate dynamic convolution blocks during the feature fusion step to enhance the high-level feature upsampling. An attention mechanism is employed to focus on the salient features of objects. We have conducted a series of experiments to validate the effectiveness of our proposed model. Notably, the proposed model achieved a 3.5% mean average precision (mAP) improvement on the satellite object detection dataset. Another feature of our approach is lightweight design. We employ group convolution to reduce the computational cost in the proposed contextual convolution module. Compared to the baseline model, our method reduces the number of parameters by 30%, computational cost by 34%, and an FPS rate close to the baseline model. We also validate the detection results through a series of visualizations.
Full article
(This article belongs to the Special Issue Emerging Research in Target Detection and Recognition in Remote Sensing Images)
Open AccessArticle
A User Study on Modeling IoT-Aware Processes with BPMN 2.0
by
Yusuf Kirikkayis, Michael Winter and Manfred Reichert
Information 2024, 15(4), 229; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040229 - 18 Apr 2024
Abstract
Integrating the Internet of Things (IoT) into business process management (BPM) aims to increase the automation level, efficiency, transparency, and comprehensibility of the business processes taking place in the physical world. The IoT enables the seamless networking of physical devices, allowing for the
[...] Read more.
Integrating the Internet of Things (IoT) into business process management (BPM) aims to increase the automation level, efficiency, transparency, and comprehensibility of the business processes taking place in the physical world. The IoT enables the seamless networking of physical devices, allowing for the enrichment of processes with real-time data about the physical world and, thus, for optimized process automation and monitoring. To realize these benefits, the modeling of IoT-aware processes needs to be appropriately supported. Despite the great attention paid to this topic, more clarity is needed about the current state of the art of corresponding modeling solutions. Capturing IoT characteristics in business process models visually or based on labels is essential to ensure effective design and communication of IoT-aware business processes. A clear discernibility of IoT characteristics can enable the precise modeling and analysis of IoT-aware processes and facilitate collaboration among different stakeholders. With an increasing number of process model elements, it becomes crucial that process model readers can understand the IoT aspects of business processes in order to make informed decisions and to optimize the processes with respect to IoT integration. This paper presents the results of a large user study (N = 249) that explored the perception of IoT aspects in BPMN 2.0 process models to gain insights into the IoT’s involvement in business processes that drive the successful implementation and communication of IoT-aware processes.
Full article
(This article belongs to the Special Issue Recent Advances in IoT and Cyber/Physical System)
►▼
Show Figures
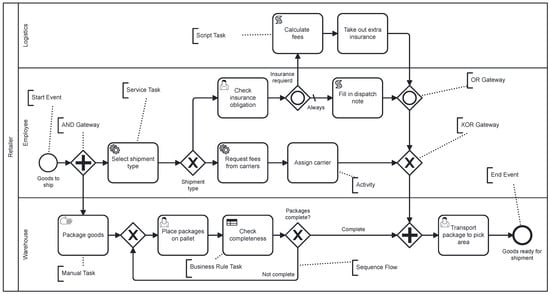
Figure 1
Open AccessArticle
Ensemble Modeling with a Bayesian Maximal Information Coefficient-Based Model of Bayesian Predictions on Uncertainty Data
by
Tisinee Surapunt and Shuliang Wang
Information 2024, 15(4), 228; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040228 - 18 Apr 2024
Abstract
Uncertainty presents unfamiliar circumstances or incomplete information that may be difficult to handle with a single model of a traditional machine learning algorithm. They are possibly limited by inadequate data, an ambiguous model, and learning performance to make a prediction. Therefore, ensemble modeling
[...] Read more.
Uncertainty presents unfamiliar circumstances or incomplete information that may be difficult to handle with a single model of a traditional machine learning algorithm. They are possibly limited by inadequate data, an ambiguous model, and learning performance to make a prediction. Therefore, ensemble modeling is proposed as a powerful model for enhancing predictive capabilities and robustness. This study aims to apply Bayesian prediction to ensemble modeling because it can encode conditional dependencies between variables and present the reasoning model using the BMIC model. The BMIC has clarified knowledge in the model which is ready for learning. Then, it was selected as the base model to be integrated with well-known algorithms such as logistic regression, K-nearest neighbors, decision trees, random forests, support vector machines (SVMs), neural networks, naive Bayes, and XGBoost classifiers. Also, the Bayesian neural network (BNN) and the probabilistic Bayesian neural network (PBN) were considered to compare their performance as a single model. The findings of this study indicate that the ensemble model of the BMIC with some traditional algorithms, which are SVM, random forest, neural networks, and XGBoost classifiers, returns 96.3% model accuracy in prediction. It provides a more reliable model and a versatile approach to support decision-making.
Full article
(This article belongs to the Special Issue New Trend on Fuzzy Systems and Intelligent Decision Making Theory: A Themed Issue Dedicated to Dr. Ronald R. Yager)
►▼
Show Figures
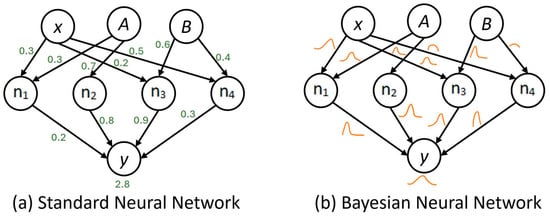
Figure 1
Open AccessArticle
An Optimized Deep Learning Approach for Detecting Fraudulent Transactions
by
Said El Kafhali, Mohammed Tayebi and Hamza Sulimani
Information 2024, 15(4), 227; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040227 - 18 Apr 2024
Abstract
►▼
Show Figures
The proliferation of new technologies and advancements in existing ones are altering our perspective of the world. So, continuous improvements are needed. A connected world filled with a vast amount of data was created as a result of the integration of these advanced
[...] Read more.
The proliferation of new technologies and advancements in existing ones are altering our perspective of the world. So, continuous improvements are needed. A connected world filled with a vast amount of data was created as a result of the integration of these advanced technologies in the financial sector. The advantages of this connection came at the cost of more sophisticated and advanced attacks, such as fraudulent transactions. To address these illegal transactions, researchers and engineers have created and implemented various systems and models to detect fraudulent transactions; many of them produce better results than others. On the other hand, criminals change their strategies and technologies to imitate legitimate transactions. In this article, the objective is to propose an intelligent system for detecting fraudulent transactions using various deep learning architectures, including artificial neural networks (ANNs), recurrent neural networks (RNNs), and long short-term memory (LSTM). Furthermore, the Bayesian optimization algorithm is used for hyperparameter optimization. For the evaluation, a credit card fraudulent transaction dataset was used. Based on the many experiments conducted, the RNN architecture demonstrated better efficiency and yielded better results in a shorter computational time than the ANN LSTM architectures.
Full article
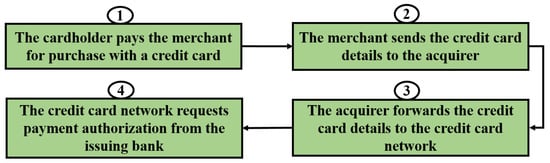
Figure 1
Open AccessArticle
Chatbot Design and Implementation: Towards an Operational Model for Chatbots
by
Alexander Skuridin and Martin Wynn
Information 2024, 15(4), 226; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040226 - 17 Apr 2024
Abstract
The recent past has witnessed a growing interest in technologies for creating chatbots. Advances in Large Language Models for natural language processing are underpinning rapid progress in chatbot development, and experts predict revolutionary changes in the labour market as many manual tasks are
[...] Read more.
The recent past has witnessed a growing interest in technologies for creating chatbots. Advances in Large Language Models for natural language processing are underpinning rapid progress in chatbot development, and experts predict revolutionary changes in the labour market as many manual tasks are replaced by virtual assistants in a range of business functions. As the new technology becomes more accessible and advanced, more companies are exploring the possibilities of implementing virtual assistants to automate routine tasks and improve service. This article reports on qualitative inductive research undertaken within a chatbot development team operating in a major international enterprise. The findings identify critical success factors for chatbot projects, and a model is developed and validated to support the planning and implementation of chatbot projects. The presented model can serve as an exemplary guide for researchers and practitioners working in this field. It is flexible and applicable in a wide range of business contexts, linking strategic business goals with execution steps. It is particularly applicable for teams with no experience in chatbot implementation, reducing uncertainty and managing decisions and risks throughout the project lifecycle, thereby increasing the likelihood of project success.
Full article
(This article belongs to the Special Issue Artificial Intelligence (AI) for Economics and Business Management)
Open AccessArticle
Economic Scheduling Model of an Active Distribution Network Based on Chaotic Particle Swarm Optimization
by
Yaxuan Xu, Jianuo Liu, Zhongqi Cui, Ziying Liu, Chenxu Dai, Xiangzhen Zang and Zhanlin Ji
Information 2024, 15(4), 225; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040225 - 17 Apr 2024
Abstract
With the continuous increase in global energy demand and growing environmental awareness, the utilization of renewable energy has become a worldwide consensus. In order to address the challenges posed by the intermittent and unpredictable nature of renewable energy in distributed power distribution networks,
[...] Read more.
With the continuous increase in global energy demand and growing environmental awareness, the utilization of renewable energy has become a worldwide consensus. In order to address the challenges posed by the intermittent and unpredictable nature of renewable energy in distributed power distribution networks, as well as to improve the economic and operational stability of distribution systems, this paper proposes the establishment of an active distribution network capable of accommodating renewable energy. The objective is to enhance the efficiency of new energy utilization. This study investigates optimal scheduling models for energy storage technologies and economic-operation dispatching techniques in distributed power distribution networks. Additionally, it develops a comprehensive demand response model, with real-time pricing and incentive policies aiming to minimize load peak–valley differentials. The control mechanism incorporates time-of-use pricing and integrates a chaos particle swarm algorithm for a holistic approach to solution finding. By coordinating and optimizing the control of distributed power sources, energy storage systems, and flexible loads, the active distribution network achieves minimal operational costs while meeting demand-side power requirements, striving to smooth out load curves as much as possible. Case studies demonstrate significant enhancements during off-peak periods, with an approximately 60% increase in the load power overall elevation of load factors during regular periods, as well as a reduction in grid loads during evening peak hours, with a maximum decrease of nearly 65 kW. This approach mitigates grid operational pressures and user expense, effectively enhancing the stability and economic efficiency in distribution network operations.
Full article
(This article belongs to the Special Issue Optimization Algorithms for Engineering Applications)
►▼
Show Figures
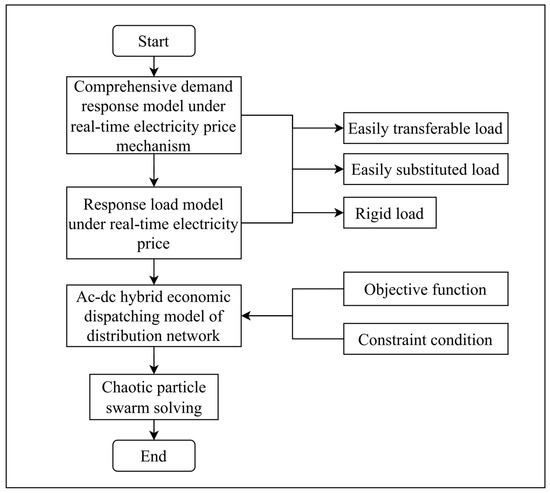
Figure 1
Open AccessArticle
Violin Music Emotion Recognition with Fusion of CNN–BiGRU and Attention Mechanism
by
Sihan Ma and Ruohua Zhou
Information 2024, 15(4), 224; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040224 - 16 Apr 2024
Abstract
►▼
Show Figures
Music emotion recognition has garnered significant interest in recent years, as the emotions expressed through music can profoundly enhance our understanding of its deeper meanings. The violin, with its distinctive emotional expressiveness, has become a focal point in this field of research. To
[...] Read more.
Music emotion recognition has garnered significant interest in recent years, as the emotions expressed through music can profoundly enhance our understanding of its deeper meanings. The violin, with its distinctive emotional expressiveness, has become a focal point in this field of research. To address the scarcity of specialized data, we developed a dataset specifically for violin music emotion recognition named VioMusic. This dataset offers a precise and comprehensive platform for the analysis of emotional expressions in violin music, featuring specialized samples and evaluations. Moreover, we implemented the CNN–BiGRU–Attention (CBA) model to establish a baseline system for music emotion recognition. Our experimental findings show that the CBA model effectively captures the emotional nuances in violin music, achieving mean absolute errors (MAE) of 0.124 and 0.129. The VioMusic dataset proves to be highly practical for advancing the study of emotion recognition in violin music, providing valuable insights and a robust framework for future research.
Full article
Figure 1
Open AccessArticle
An Extensive Performance Comparison between Feature Reduction and Feature Selection Preprocessing Algorithms on Imbalanced Wide Data
by
Ismael Ramos-Pérez, José Antonio Barbero-Aparicio, Antonio Canepa-Oneto, Álvar Arnaiz-González and Jesús Maudes-Raedo
Information 2024, 15(4), 223; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040223 - 16 Apr 2024
Abstract
The most common preprocessing techniques used to deal with datasets having high dimensionality and a low number of instances—or wide data—are feature reduction (FR), feature selection (FS), and resampling. This study explores the use of FR and resampling techniques, expanding the limited comparisons
[...] Read more.
The most common preprocessing techniques used to deal with datasets having high dimensionality and a low number of instances—or wide data—are feature reduction (FR), feature selection (FS), and resampling. This study explores the use of FR and resampling techniques, expanding the limited comparisons between FR and filter FS methods in the existing literature, especially in the context of wide data. We compare the optimal outcomes from a previous comprehensive study of FS against new experiments conducted using FR methods. Two specific challenges associated with the use of FR are outlined in detail: finding FR methods that are compatible with wide data and the need for a reduction estimator of nonlinear approaches to process out-of-sample data. The experimental study compares 17 techniques, including supervised, unsupervised, linear, and nonlinear approaches, using 7 resampling strategies and 5 classifiers. The results demonstrate which configurations are optimal, according to their performance and computation time. Moreover, the best configuration—namely, k Nearest Neighbor (KNN) + the Maximal Margin Criterion (MMC) feature reducer with no resampling—is shown to outperform state-of-the-art algorithms.
Full article
(This article belongs to the Special Issue Machine Learning Approaches for Imbalanced Domains: Emerging Trends and Applications)
Open AccessArticle
Time Series Forecasting with Missing Data Using Generative Adversarial Networks and Bayesian Inference
by
Xiaoou Li
Information 2024, 15(4), 222; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040222 - 15 Apr 2024
Abstract
This paper tackles the challenge of time series forecasting in the presence of missing data. Traditional methods often struggle with such data, which leads to inaccurate predictions. We propose a novel framework that combines the strengths of Generative Adversarial Networks (GANs) and Bayesian
[...] Read more.
This paper tackles the challenge of time series forecasting in the presence of missing data. Traditional methods often struggle with such data, which leads to inaccurate predictions. We propose a novel framework that combines the strengths of Generative Adversarial Networks (GANs) and Bayesian inference. The framework utilizes a Conditional GAN (C-GAN) to realistically impute missing values in the time series data. Subsequently, Bayesian inference is employed to quantify the uncertainty associated with the forecasts due to the missing data. This combined approach improves the robustness and reliability of forecasting compared to traditional methods. The effectiveness of our proposed method is evaluated on a real-world dataset of air pollution data from Mexico City. The results demonstrate the framework’s capability to handle missing data and achieve improved forecasting accuracy.
Full article
(This article belongs to the Special Issue New Deep Learning Approach for Time Series Forecasting)
►▼
Show Figures
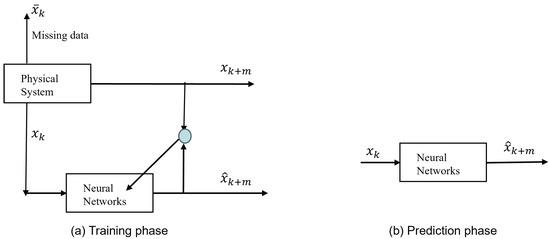
Figure 1
Open AccessArticle
Phase Noise Effects on OFDM Chirp Communication Systems: Characteristics and Compensation
by
Mengjiao Li and Wenqin Wang
Information 2024, 15(4), 221; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040221 - 14 Apr 2024
Abstract
Orthogonal frequency-division multiplexing (OFDM) chirp waveforms are an attractive candidate to be a dual-function signal scheme for the joint radar and communication systems. OFDM chirp signals can not only be employed to transmit communication data through classic phase modulation, but also can perform
[...] Read more.
Orthogonal frequency-division multiplexing (OFDM) chirp waveforms are an attractive candidate to be a dual-function signal scheme for the joint radar and communication systems. OFDM chirp signals can not only be employed to transmit communication data through classic phase modulation, but also can perform radar detection by applying linear frequency modulation for subcarriers. However, the performance of the OFDM chirp communication system under the phase noise environment still remains uninvestigated. This paper tries to discuss the influence of phase noise on OFDM chirp communication systems and proposes effective phase noise estimation and compensation methods. We find that the phase noise effect on OFDM chirp communication systems consists of a common phase error (CPE) and an inter-carrier interference (ICI). If not compensated, the performance of the dual-function systems can be seriously degraded. In particular, an exact expression for the signal-plus-interference to noise ratio (SINR) for the OFDM chirp communication system is derived and some critical parameters are analyzed to exhibit the phase noise effects on system performance. Moreover, two low-complexity estimation approaches, maximum likelihood (ML) and linear minimum mean square error (LMMSE), as well as two compensation approaches, the de-correlation and cancellation algorithms, are respectively utilized to eliminate the phase noise impairment. Finally, the phase noise effects and the effectiveness of the compensation approach are verified by extensive numerical results.
Full article
(This article belongs to the Section Information Systems)
►▼
Show Figures

Figure 1
Open AccessArticle
Early Parkinson’s Disease Diagnosis through Hand-Drawn Spiral and Wave Analysis Using Deep Learning Techniques
by
Yingcong Huang, Kunal Chaturvedi, Al-Akhir Nayan, Mohammad Hesam Hesamian, Ali Braytee and Mukesh Prasad
Information 2024, 15(4), 220; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040220 - 13 Apr 2024
Abstract
Parkinson’s disease (PD) is a chronic brain disorder affecting millions worldwide. It occurs when brain cells that produce dopamine, a chemical controlling movement, die or become damaged. This leads to PD, which causes problems with movement, balance, and posture. Early detection is crucial
[...] Read more.
Parkinson’s disease (PD) is a chronic brain disorder affecting millions worldwide. It occurs when brain cells that produce dopamine, a chemical controlling movement, die or become damaged. This leads to PD, which causes problems with movement, balance, and posture. Early detection is crucial to slow its progression and improve the quality of life for PD patients. This paper proposes a handwriting-based prediction approach combining a cosine annealing scheduler with deep transfer learning. It utilizes the NIATS dataset, which contains handwriting samples from individuals with and without PD, to evaluate six different models: VGG16, VGG19, ResNet18, ResNet50, ResNet101, and Vit. This paper compares the performance of these models based on three metrics: accuracy, precision, and F1 score. The results showed that the VGG19 model, combined with the proposed method, achieved the highest average accuracy of 96.67%.
Full article
(This article belongs to the Special Issue Editorial Board Members’ Collection Series: "Information Processes")
►▼
Show Figures
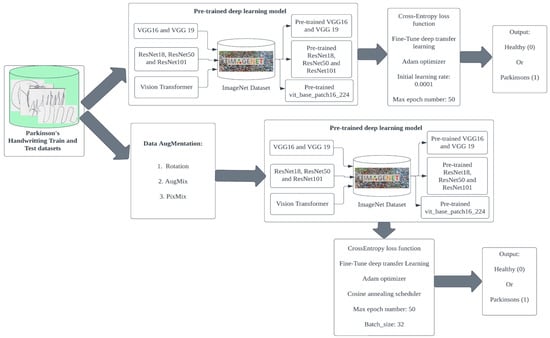
Figure 1
Open AccessArticle
A Proactive Decision-Making Model for Evaluating the Reliability of Infrastructure Assets of a Railway System
by
Daniel O. Aikhuele and Shahryar Sorooshian
Information 2024, 15(4), 219; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040219 - 13 Apr 2024
Abstract
Railway infrastructure is generally classified as either fixed or movable infrastructure assets. Failure in any of the assets could lead to the complete shutdown and disruption of the entire system, economic loss, inconvenience to passengers and the train operating company(s), and can sometimes
[...] Read more.
Railway infrastructure is generally classified as either fixed or movable infrastructure assets. Failure in any of the assets could lead to the complete shutdown and disruption of the entire system, economic loss, inconvenience to passengers and the train operating company(s), and can sometimes result in death or injury in the event of the derailment of the rolling stock. Considering the importance of the railway infrastructure assets, it is only necessary to continuously explore their behavior, reliability, and safety. In this paper, a proactive multi-criteria decision-making model that is based on an interval-valued intuitionistic fuzzy set and some reliability quantitative parameters has been proposed for the evaluation of the reliability of the infrastructure assets. Results from the evaluation show that the failure mode ‘Broken and defective rails’ has the most risk and reliability concerns. Hence, priority should be given to the failure mode to avoid a total system collapse.
Full article
(This article belongs to the Special Issue Second Edition of Predictive Analytics and Data Science)
►▼
Show Figures
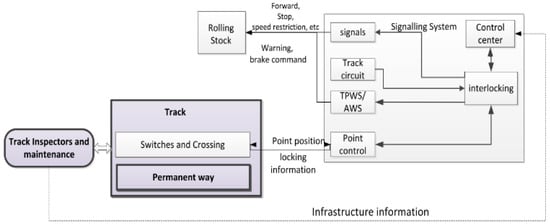
Figure 1
Open AccessArticle
Using ML to Predict User Satisfaction with ICT Technology for Educational Institution Administration
by
Hamad Almaghrabi, Ben Soh and Alice Li
Information 2024, 15(4), 218; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040218 - 12 Apr 2024
Abstract
Effective and efficient use of information and communication technology (ICT) systems in the administration of educational organisations is crucial to optimise their performance. Earlier research on the identification and analysis of ICT users’ satisfaction with administration tasks in education is limited and inconclusive,
[...] Read more.
Effective and efficient use of information and communication technology (ICT) systems in the administration of educational organisations is crucial to optimise their performance. Earlier research on the identification and analysis of ICT users’ satisfaction with administration tasks in education is limited and inconclusive, as they focus on using ICT for nonadministrative tasks. To address this gap, this study employs Artificial Intelligence (AI) and machine learning (ML) in conjunction with a survey technique to predict the satisfaction of ICT users. In doing so, it provides an insight into the key factors that impact users’ satisfaction with the ICT administrative systems. The results reveal that AI and ML models predict ICT user satisfaction with an accuracy of 94%, and identify the specific ICT features, such as usability, privacy, security, and Information Technology (IT) support as key determinants of satisfaction. The ability to predict user satisfaction is important as it allows organisations to make data-driven decisions on improving their ICT systems to better meet the needs and expectations of users, maximising labour effort while minimising resources, and identifying potential issues earlier. The findings of this study have important implications for the use of ML in improving the administration of educational institutions and providing valuable insights for decision-makers and developers.
Full article
(This article belongs to the Special Issue Artificial Intelligence (AI) for Economics and Business Management)
►▼
Show Figures
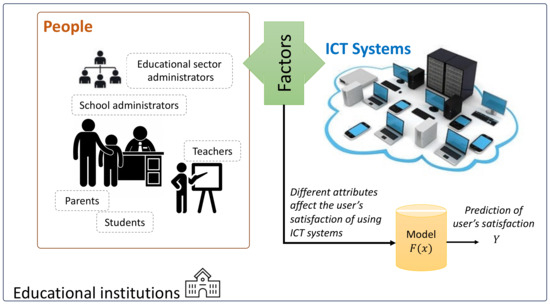
Figure 1
Open AccessArticle
Predicting Individual Well-Being in Teamwork Contexts Based on Speech Features
by
Tobias Zeulner, Gerhard Johann Hagerer, Moritz Müller, Ignacio Vazquez and Peter A. Gloor
Information 2024, 15(4), 217; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040217 - 12 Apr 2024
Abstract
Current methods for assessing individual well-being in team collaboration at the workplace often rely on manually collected surveys. This limits continuous real-world data collection and proactive measures to improve team member workplace satisfaction. We propose a method to automatically derive social signals related
[...] Read more.
Current methods for assessing individual well-being in team collaboration at the workplace often rely on manually collected surveys. This limits continuous real-world data collection and proactive measures to improve team member workplace satisfaction. We propose a method to automatically derive social signals related to individual well-being in team collaboration from raw audio and video data collected in teamwork contexts. The goal was to develop computational methods and measurements to facilitate the mirroring of individuals’ well-being to themselves. We focus on how speech behavior is perceived by team members to improve their well-being. Our main contribution is the assembly of an integrated toolchain to perform multi-modal extraction of robust speech features in noisy field settings and to explore which features are predictors of self-reported satisfaction scores. We applied the toolchain to a case study, where we collected videos of 20 teams with 56 participants collaborating over a four-day period in a team project in an educational environment. Our audiovisual speaker diarization extracted individual speech features from a noisy environment. As the dependent variable, team members filled out a daily PERMA (positive emotion, engagement, relationships, meaning, and accomplishment) survey. These well-being scores were predicted using speech features extracted from the videos using machine learning. The results suggest that the proposed toolchain was able to automatically predict individual well-being in teams, leading to better teamwork and happier team members.
Full article
(This article belongs to the Special Issue Advances in Explainable Artificial Intelligence, 2nd Edition)
►▼
Show Figures

Figure 1
Open AccessArticle
There Are Infinite Ways to Formulate Code: How to Mitigate the Resulting Problems for Better Software Vulnerability Detection
by
Jinghua Groppe, Sven Groppe, Daniel Senf and Ralf Möller
Information 2024, 15(4), 216; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040216 - 11 Apr 2024
Abstract
Given a set of software programs, each being labeled either as vulnerable or benign, deep learning technology can be used to automatically build a software vulnerability detector. A challenge in this context is that there are countless equivalent ways to implement a particular
[...] Read more.
Given a set of software programs, each being labeled either as vulnerable or benign, deep learning technology can be used to automatically build a software vulnerability detector. A challenge in this context is that there are countless equivalent ways to implement a particular functionality in a program. For instance, the naming of variables is often a matter of the personal style of programmers, and thus, the detection of vulnerability patterns in programs is made difficult. Current deep learning approaches to software vulnerability detection rely on the raw text of a program and exploit general natural language processing capabilities to address the problem of dealing with different naming schemes in instances of vulnerability patterns. Relying on natural language processing, and learning how to reveal variable reference structures from the raw text, is often too high a burden, however. Thus, approaches based on deep learning still exhibit problems generating a detector with decent generalization properties due to the naming or, more generally formulated, the vocabulary explosion problem. In this work, we propose techniques to mitigate this problem by making the referential structure of variable references explicit in input representations for deep learning approaches. Evaluation results show that deep learning models based on techniques presented in this article outperform raw text approaches for vulnerability detection. In addition, the new techniques also induce a very small main memory footprint. The efficiency gain of memory usage can be up to four orders of magnitude compared to existing methods as our experiments indicate.
Full article
(This article belongs to the Section Artificial Intelligence)
►▼
Show Figures
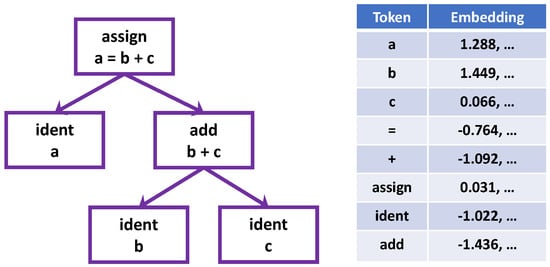
Figure 1
Open AccessArticle
LighterFace Model for Community Face Detection and Recognition
by
Yuntao Shi, Hongfei Zhang, Wei Guo, Meng Zhou, Shuqin Li, Jie Li and Yu Ding
Information 2024, 15(4), 215; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040215 - 11 Apr 2024
Abstract
►▼
Show Figures
This research proposes a face detection algorithm named LighterFace, which is aimed at enhancing detection speed to meet the demands of real-time community applications. Two pre-trained convolutional neural networks are combined, namely Cross Stage Partial Network (CSPNet), and ShuffleNetv2. Connecting the optimized network
[...] Read more.
This research proposes a face detection algorithm named LighterFace, which is aimed at enhancing detection speed to meet the demands of real-time community applications. Two pre-trained convolutional neural networks are combined, namely Cross Stage Partial Network (CSPNet), and ShuffleNetv2. Connecting the optimized network with Global Attention Mechanism (GAMAttention) extends the model to compensate for the accuracy loss caused by optimizing the network structure. Additionally, the learning rate of the detection model is dynamically updated using the cosine annealing method, which enhances the convergence speed of the model during training. This paper analyzes the training of the LighterFace model on the WiderFace dataset and a custom community dataset, aiming to classify faces in real-life community settings. Compared to the mainstream YOLOv5 model, LighterFace demonstrates a significant reduction in computational demands by 85.4% while achieving a 66.3% increase in detection speed and attaining a 90.6% accuracy in face detection. It is worth noting that LighterFace generates high-quality cropped face images, providing valuable inputs for subsequent face recognition models such as DeepID. Additionally, the LighterFace model is specifically designed to run on edge devices with lower computational capabilities. Its real-time performance on a Raspberry Pi 3B+ validates the results.
Full article
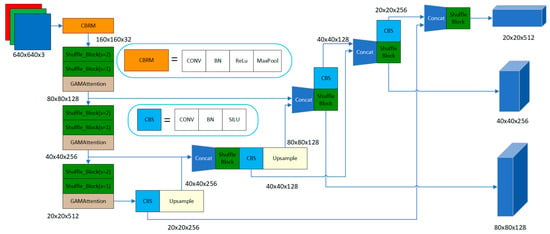
Figure 1
Open AccessArticle
Automated Mapping of Common Vulnerabilities and Exposures to MITRE ATT&CK Tactics
by
Ioana Branescu, Octavian Grigorescu and Mihai Dascalu
Information 2024, 15(4), 214; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040214 - 10 Apr 2024
Abstract
Effectively understanding and categorizing vulnerabilities is vital in the ever-evolving cybersecurity landscape, since only one exposure can have a devastating effect on the entire system. Given the increasingly massive number of threats and the size of modern infrastructures, the need for structured, uniform
[...] Read more.
Effectively understanding and categorizing vulnerabilities is vital in the ever-evolving cybersecurity landscape, since only one exposure can have a devastating effect on the entire system. Given the increasingly massive number of threats and the size of modern infrastructures, the need for structured, uniform cybersecurity knowledge systems arose. To tackle this challenge, the MITRE Corporation set up two powerful sources of cyber threat and vulnerability information, namely the Common Vulnerabilities and Exposures (CVEs) list focused on identifying and fixing software vulnerabilities, and the MITRE ATT&CK Enterprise Matrix, which is a framework for defining and categorizing adversary actions and ways to defend against them. At the moment, the two are not directly linked, even if such a link would have a significant positive impact on the cybersecurity community. This study aims to automatically map CVEs to the corresponding 14 MITRE ATT&CK tactics using state-of-the-art transformer-based models. Various architectures, from encoders to generative large-scale models, are employed to tackle this multilabel classification problem. Our results are promising, with a SecRoBERTa model performing best with an F1 score of 77.81%, which is closely followed by SecBERT (78.77%), CyBERT (78.54%), and TARS (78.01%), while GPT-4 showed a weak performance in zero-shot settings (22.04%). In addition, we perform an in-depth error analysis to better understand the models’ performance and limitations. We release the code used for all experiments as open source.
Full article
(This article belongs to the Special Issue Advances in Cybersecurity and Reliability)
►▼
Show Figures
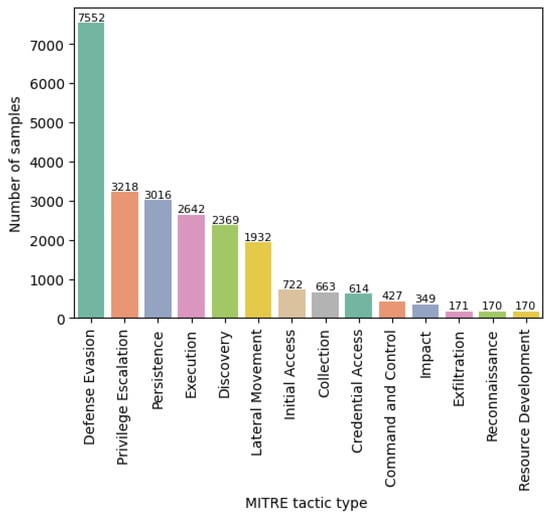
Figure 1
Open AccessArticle
A Flexible Infrastructure-Sharing 5G Network Architecture Based on Network Slicing and Roaming
by
João P. Ferreira, Vinicius C. Ferreira, Sérgio L. Nogueira, João M. Faria and José A. Afonso
Information 2024, 15(4), 213; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040213 - 10 Apr 2024
Abstract
The sharing of mobile network infrastructure has become a key topic with the introduction of 5G due to the high costs of deploying such infrastructures, with neutral host models coupled with features such as network function virtualization (NFV) and network slicing emerging as
[...] Read more.
The sharing of mobile network infrastructure has become a key topic with the introduction of 5G due to the high costs of deploying such infrastructures, with neutral host models coupled with features such as network function virtualization (NFV) and network slicing emerging as viable solutions for the challenges in this area. With this in mind, this work presents the design, implementation, and test of a flexible infrastructure-sharing 5G network architecture capable of providing services to any type of client, whether an operator or not. The proposed architecture leverages 5G’s network slicing for traffic isolation and compliance with the policies of different clients, with roaming employed for the authentication of users of operator clients. The proposed architecture was implemented and tested in a simulation environment using the UERANSIM and Open5GS open-source tools. Qualitative tests successfully validated the authentication and the traffic isolation features provided by the slices for the two types of clients. Results also demonstrate that the proposed architecture has a positive impact on the performance of the neutral host network infrastructure, achieving 61.8%-higher throughput and 96.8%-lower packet loss ratio (PLR) in a scenario sharing the infrastructure among four clients and eight users when compared to a single client with all the network resources.
Full article
(This article belongs to the Special Issue Wireless IoT Network Protocols II)
►▼
Show Figures
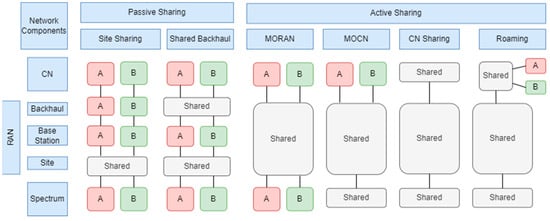
Figure 1
Open AccessArticle
Blockchain-Enhanced Sensor-as-a-Service (SEaaS) in IoT: Leveraging Blockchain for Efficient and Secure Sensing Data Transactions
by
Burhan Ul Islam Khan, Khang Wen Goh, Mohammad Shuaib Mir, Nur Fatin Liyana Mohd Rosely, Aabid Ahmad Mir and Mesith Chaimanee
Information 2024, 15(4), 212; https://0-doi-org.brum.beds.ac.uk/10.3390/info15040212 - 10 Apr 2024
Abstract
►▼
Show Figures
As the Internet of Things (IoT) continues to revolutionize value-added services, its conventional architecture exhibits persistent scalability and security vulnerabilities, jeopardizing the trustworthiness of IoT-based services. These architectural limitations hinder the IoT’s Sensor-as-a-Service (SEaaS) model, which enables the commercial transmission of sensed data
[...] Read more.
As the Internet of Things (IoT) continues to revolutionize value-added services, its conventional architecture exhibits persistent scalability and security vulnerabilities, jeopardizing the trustworthiness of IoT-based services. These architectural limitations hinder the IoT’s Sensor-as-a-Service (SEaaS) model, which enables the commercial transmission of sensed data through cloud platforms. This study proposes an innovative computational framework that integrates decentralized blockchain technology into the IoT architectural design, specifically enhancing SEaaS efficiency. This research contributes to an optimized IoT architecture with decentralized blockchain operations and simplified public key encryption. Furthermore, this study introduces an advanced SEaaS model featuring innovative trading operations for sensed data among diverse stakeholders. At its core, this model presents a unique blockchain-based data-sharing mechanism that manages multiple aspects, from enrollment to validation. Evaluations conducted in a standard Python environment indicate that the proposed SEaaS model outperforms existing blockchain-based data-sharing models, demonstrating approximately 40% less energy consumption, 18% increased throughput, 16% reduced latency, and a 25% reduction in algorithm processing time. Ultimately, integrating a lightweight authentication mechanism using simplified public key cryptography within the blockchain establishes the model’s potential for efficient and secure data-sharing in IoT.
Full article
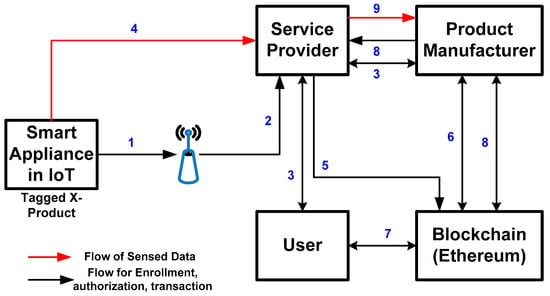
Figure 1

Journal Menu
► ▼ Journal Menu-
- Information Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
AI, Algorithms, BDCC, Future Internet, Informatics, Information, Languages, Publications
AI Chatbots: Threat or Opportunity?
Topic Editors: Antony Bryant, Roberto Montemanni, Min Chen, Paolo Bellavista, Kenji Suzuki, Jeanine Treffers-DallerDeadline: 30 April 2024
Topic in
Applied Sciences, Drones, Information, Sensors
Recent Advances and Technologies in Emergency Response, Security and Disaster Management Applications
Topic Editors: Evangelos Maltezos, Eleftherios Ouzounoglou, Panagiotis Michalis, Angelos Amditis, Stefanos Vrochidis, Norman Kerle, Christos NtanosDeadline: 20 May 2024
Topic in
Algorithms, Diagnostics, Entropy, Information, J. Imaging
Application of Machine Learning in Molecular Imaging
Topic Editors: Allegra Conti, Nicola Toschi, Marianna Inglese, Andrea Duggento, Matthew Grech-Sollars, Serena Monti, Giancarlo Sportelli, Pietro CarraDeadline: 31 May 2024
Topic in
Drones, Electronics, Future Internet, Information, Mathematics
Future Internet Architecture: Difficulties and Opportunities
Topic Editors: Peiying Zhang, Haotong Cao, Keping YuDeadline: 30 June 2024

Conferences
Special Issues
Special Issue in
Information
Intelligent Agent and Multi-Agent System
Guest Editor: Katsuhide FujitaDeadline: 20 April 2024
Special Issue in
Information
New Trend on Fuzzy Systems and Intelligent Decision Making Theory: A Themed Issue Dedicated to Dr. Ronald R. Yager
Guest Editors: Luis Martínez López, Lesheng Jin, Zhen-Song Chen, Humberto BustinceDeadline: 30 April 2024
Special Issue in
Information
AI Applications in Construction and Infrastructure
Guest Editor: Sudipta ChowdhuryDeadline: 15 May 2024
Special Issue in
Information
Health Data Information Retrieval
Guest Editors: Mario Ciampi, Mario SicuranzaDeadline: 31 May 2024
Topical Collections
Topical Collection in
Information
Natural Language Processing and Applications: Challenges and Perspectives
Collection Editor: Diego Reforgiato Recupero
Topical Collection in
Information
Knowledge Graphs for Search and Recommendation
Collection Editors: Pierpaolo Basile, Annalina Caputo
Topical Collection in
Information
Augmented Reality Technologies, Systems and Applications
Collection Editors: N.D. Duque-Mendez, Ramon Fabregat, Jorge Bacca-Acosta




