An Attribute-Based Access Control for IoT Using Blockchain and Smart Contracts
Abstract
:1. Introduction
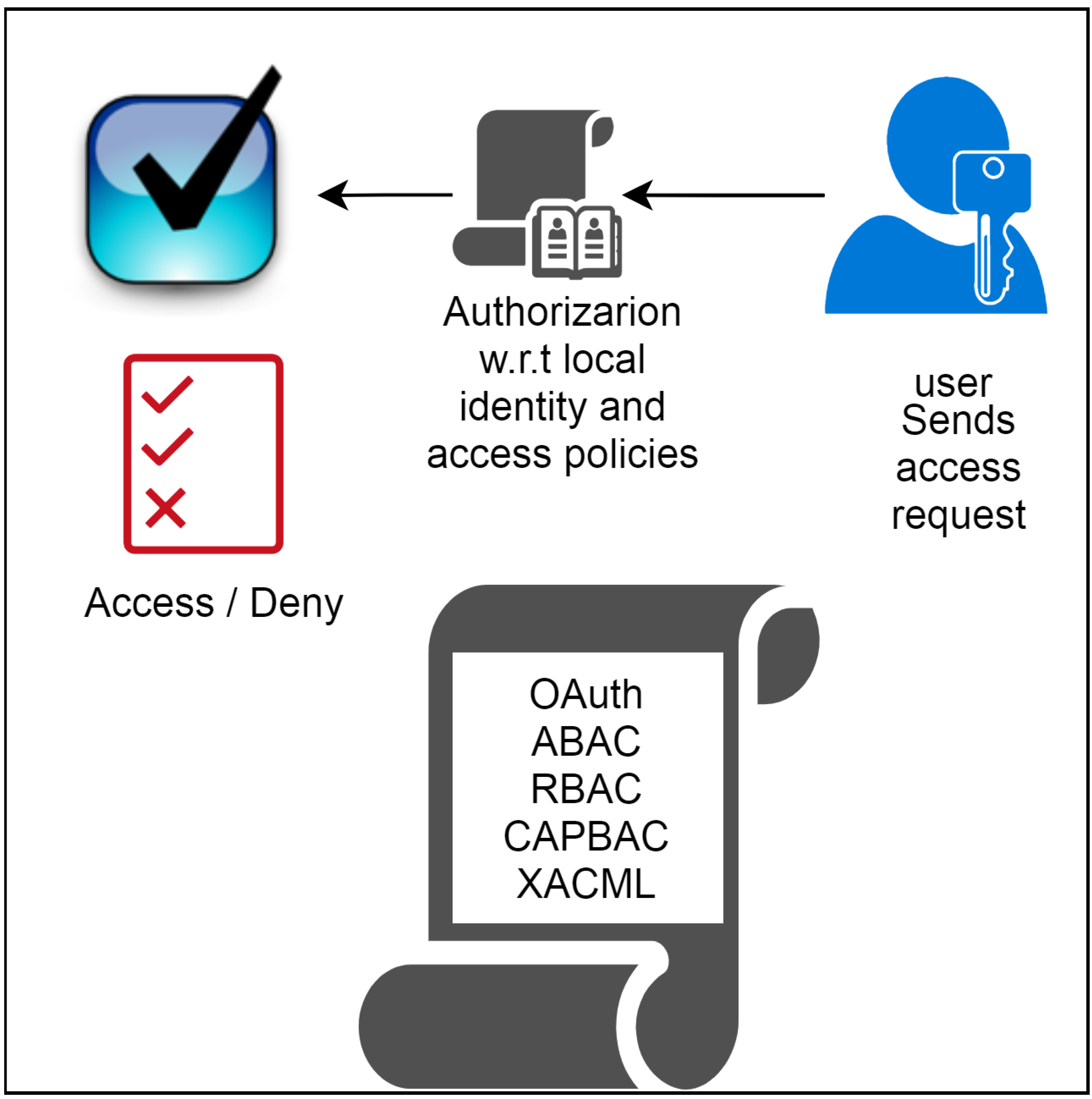
1.1. Attribute-Based Access Control (ABAC)
1.2. Paper Contributions
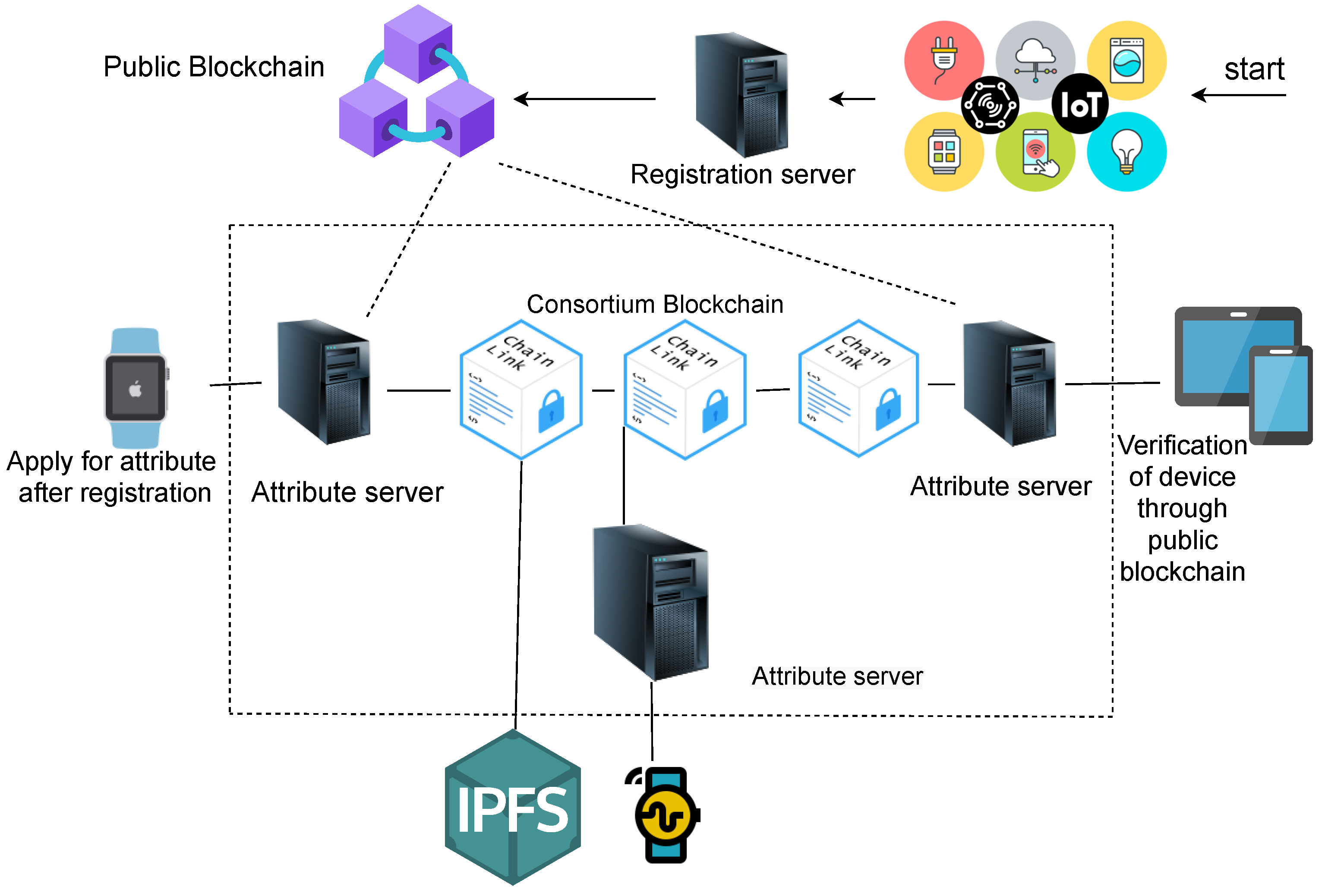
- We propose a blockchain-based network for reliable data sharing between resource-constrained IoTs.
- Storing the huge data generated by IoTs, a distributed file system, i.e., IPFS or swarm, is used.
- Proof of Authority (PoA) is used instead of Proof of Work (PoW), which increases throughput and reduces the system latency.
- A smart-contract-based access control mechanism is implemented to securely share data.
- Through smart contracts, the data ciphertext can be stored in the blockchain by the data owner.
- Data can only be decrypted in a valid access period given by the data owner.
- In blockchains, the trace function is achieved by the storage of invocation and the creation of smart contracts.
- Validating the effectiveness of cpabe and the access model, extensive simulations are performed in pylab, and the performance parameters are the total cost consumption and cpu utilization.
- To resolve the scalability issues, different kinds of blockchains have been used for data storing and data sharing.
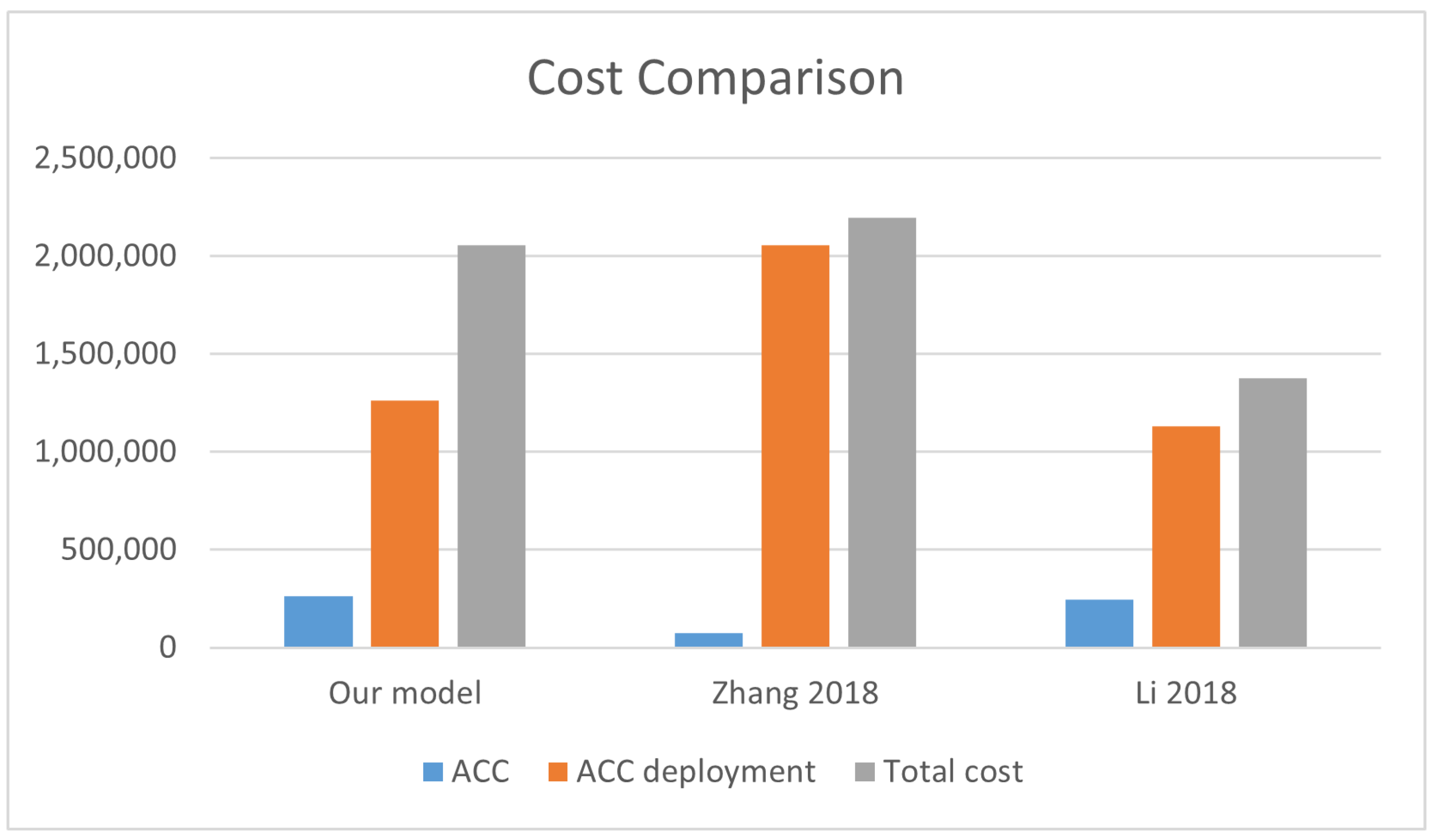
- The simulation results show that our proposed scheme significantly reduces the execution and transaction cost as well as the verification time of the transaction in a blockchain.
2. Background and Motivation
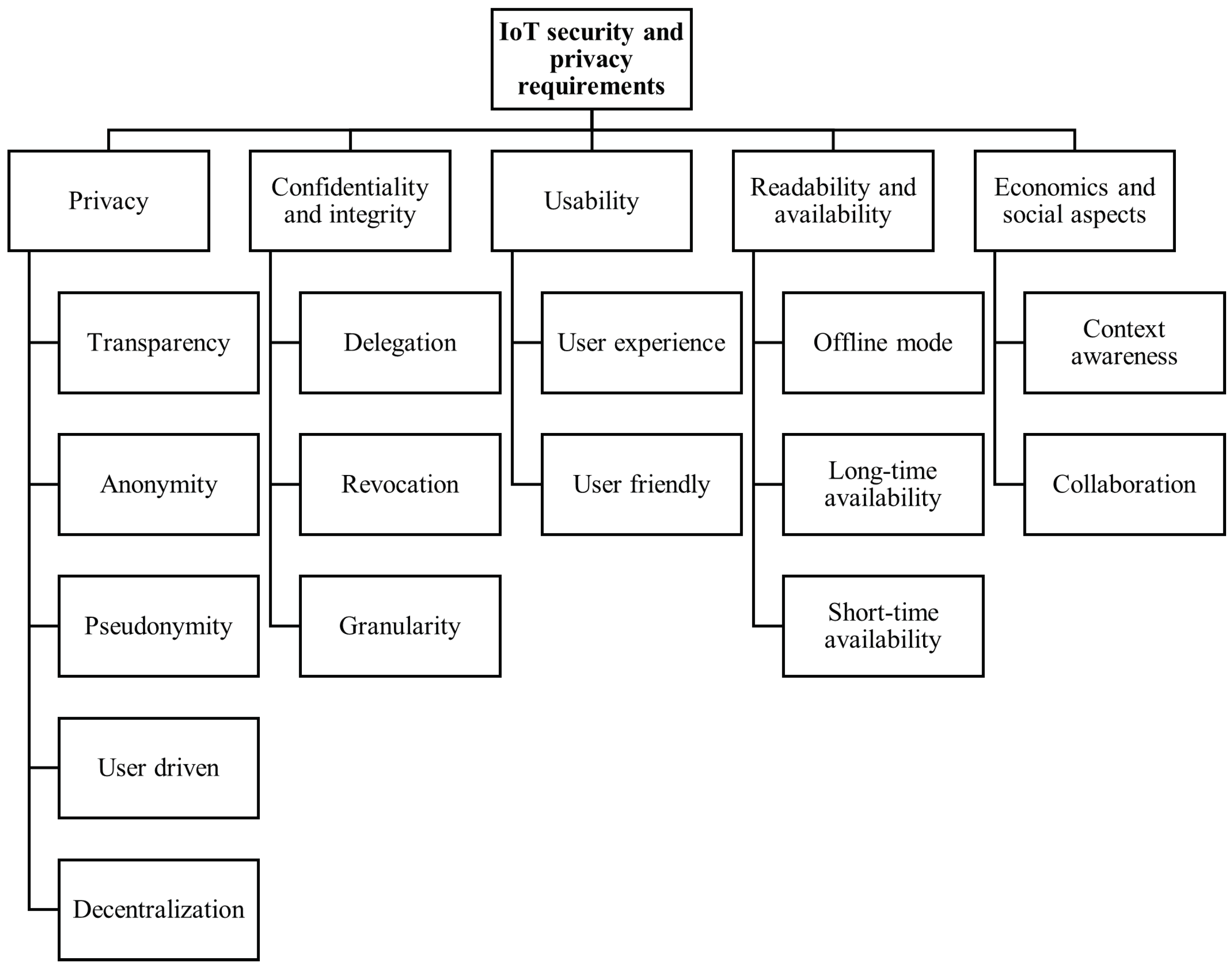
2.1. Existing Access Control IoT Architectures and Related Challenges
2.1.1. Centralized Architecture
2.1.2. Trust Entity with Decentralized Architecture
2.1.3. Distributed Architecture
2.2. Issues Faced by the Present Architectures
- Cost: Due to two main reasons, the IoT solutions are expensive:
- -
- Infrastructure cost: There are billions of connected IoT devices that generate and store a huge amount of data, while the servers are required for their interconnected communication costs and the analytical processing.
- -
- High maintenance: Updating the software in the millions of IoT devices that have a centralized cloud architecture and huge network equipment requires a high maintenance cost.
- Scalability: The huge amount of IoT devices’ data generation and processing (big data) causes a bottleneck to scaling the centralized IoT architectures. Data acquisition, transmission, and storage can be handled by these application platforms.
- Single point of failure: In critical healthcare systems, it is very important to collect the data timely. However, in cloud servers, a single point of failure may cause the whole network to shut down.
- Lack of Transparency: Transparent security architecture needs to be developed because of service providers’ irrefutable lack of trust for data collection by the millions of IoT devices in centralized models.
- Insufficient security: A huge amount of connected insecure devices on the internet is a major challenge in IoT privacy and security due to recent DoS attacks [48].
3. Preliminaries
3.1. Blockchain
3.2. Multichain
- To permit the selected transactions only;
- To permit the selected participants to see the blockchain’s activities;
- To conduct mining securely and without the associated costs of proof of work.
3.3. Smart Contracts
- The negotiation of terms;
- Automatic verification;
- Agreed terms execution.
4. Related Work
4.1. Ethereum-Based Existing Access Control Schemes
4.2. Cipher-Text-Policy-Based Attribute-Based Encryption (CP-ABE) Schemes
5. System Model and Proposed Methodology
5.1. Smart Contract System
5.2. Access Control Contract (ACC)
5.3. Subject Attribute Management Contract (SAMC)
5.4. Object Attribute Management Contract (OAMC)
5.5. Policy Management Contract (PMC)
5.6. Data Sharing Model
6. Policy Model
- 1
- Data owner: Upload encrypted data with assigning attributes sets and access control policies and is responsible for the creation and deployment of smart contracts.
- 2
- Data user: Access the encrypted data stored on IPFS. After satisfying access control polices and attribute sets, the secret key is obtained, which decrypts the encrypted data.
- 3
- IPFS: Used for the storage of encrypted data that can be stored by the data owners.
- 4
- Ethereum: To store and retrieve the data, smart contracts have been deployed on the Ethereum blockchain.
- After the device and user registration process using blockchain technology [65], the data owner uploads the encrypted data with access control policies in smart contracts.
- The returned contract address with the encrypted data hash would be stored on IPFS.
- The path of data stored in the IPFS location can be returned to the data owner.
- In Ethereum, the encrypted data key has been stored in ciphertext format.
- When the data retriever sends the access request using the timely CP-ABE, the data owner adds the policies under the effective period, encrypts the secret key, and stores it in a smart contract.
- The data retriever that satisfies the access policies in an effective period of time downloads the data and obtains the secret key from the contract.
6.1. Attribute-Based Encryption
6.2. Access Policy
- Access policy P is a rule in ABE that returns either 0 or 1.
- Attributes set is A (A1, A2, …, Am).
- If P answers 1 on A, only then can we say A satisfies P.
- Usually, to represent the fact that A satisfies P, the notation A = P is used.
- The case that A does not satisfy R is denoted as A!= P.
- We consider the AND gate policy in our construction.
- If Ai = Pi or Pi=* for all 1 <= i <= m, we say A = P; otherwise, A!= P.
- It is noted that the wildcard * in P plays the role of a “do not care” value.
- access policy P = (Clinic: 1; physician; *; Pakistan);
- a attributes set A1 = (Clinic: 1; physician; male; Pakistan);
- A2 = (Clinic: 1; Nurse; male; Pakistan);
- A1 = P, A2 != P.
- Attribute Subject = (userId, role, group);
- Attribute Object = (deviceId, MAC);
- Attribute Permission = (1, allow 0, deny);
- Attribute Environment = (createTime, endTime, allowed).
- 1.
- Setup (PK, SK):
- 2.
- Encrypt (PK, T, sek)-> CT
- 3.
- KeyGen(sk, A) -> PrK
- 4.
- Decrypt (PK, sk, CT) -> sek
7. Security Assumptions and Attacker Model
- Consistency of blockchain over nodes and timing: Blockchain transactions are accepted by the nodes present in the network.
- Growth of the blockchain: The eventual integration of valid transactions into the blockchain.
- Reliable and trustworthy gateway: The trustworthy and accessible gateway is assumed.
- Trusted entities: Attribute servers and certification authority are trusted.
- Security of keys in the blockchain: Keys are secure and cannot be lost or stolen.
- Strong cryptographic measures: Cryptographic primitives, hashes, and signatures are not broken.
- Privilege Elevation: The attacker convinces the device by declaring himself an authenticated attribute entity and promoting a fake attribute-issuing entity. He also replays a valid transaction previously performed by an attribute entity.
- Identity Revealing Attack: To reveal the real identity of authorized devices and personal data collection, the malicious entity tries to target the devices.
- Man-in-the-Middle Attack: The interception of shared data and data tempering by the malicious node between the IoT nodes and attribute servers.
- Forgery Attack: The malicious attribute server has fake keys and signatures of an authentic user and transfers it to other entities to affect the network.
- Privacy preservation: Crypto ID has been used for the communication between the entities present in our model. To enhance the privacy, we are not using the device’s real identification number as its identity. All the transactions are done in an encrypted format that preserves the identities of the users and devices.
- Data Confidentiality: Using symmetric key encryption, the communication between the IoT devices are encrypted, which enhances the security and prevents tempering of communication data.
- Data Integrity: Data generated by IoT devices are encrypted using symmetric key encryption and stored in IPFS (an example of distributed file system). To provide data integrity, we encrypt the data under a certain cipher-text-policy-based encryption, and its hashes are stored in the blockchain so that data tempering is not possible.
- Single Point of Failure: A distributed file system and multiple attribute servers have been used in our model, which eliminate the single point of failure. The attribute servers only interact with the devices of their associated identities, which enhances the system security.
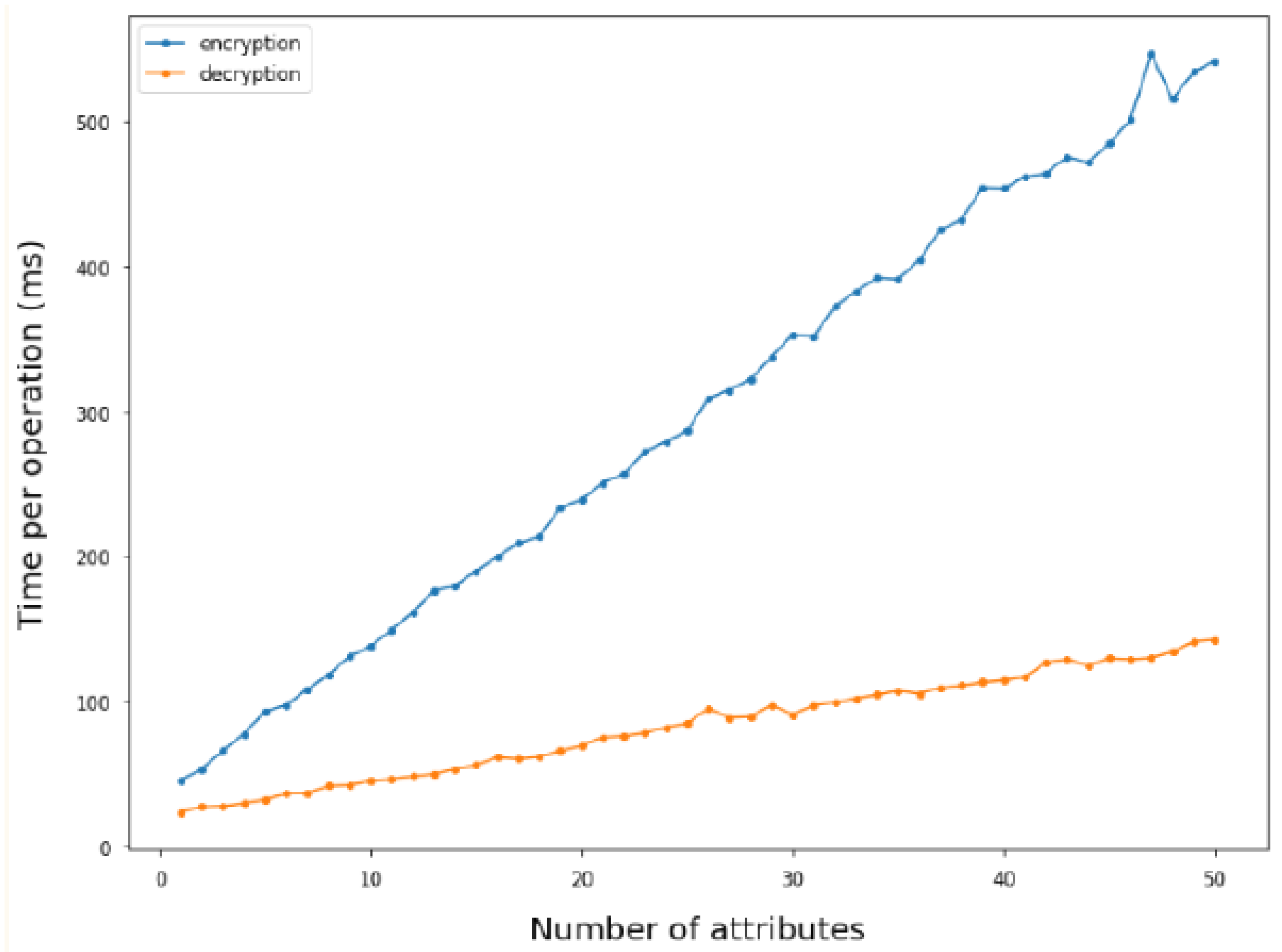
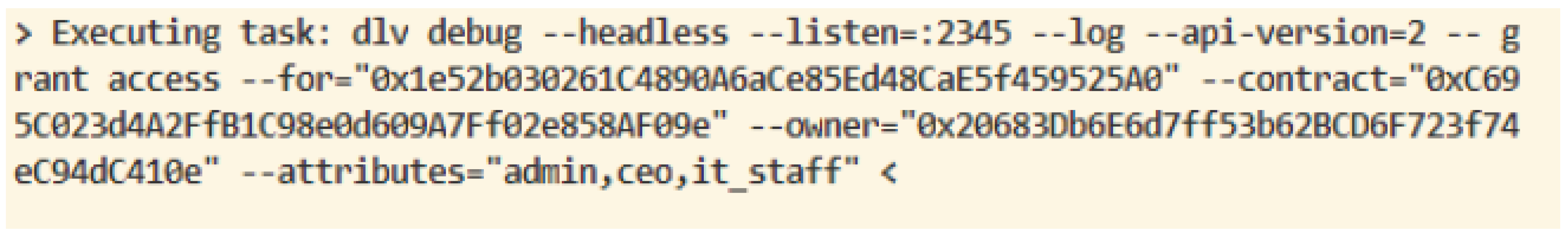
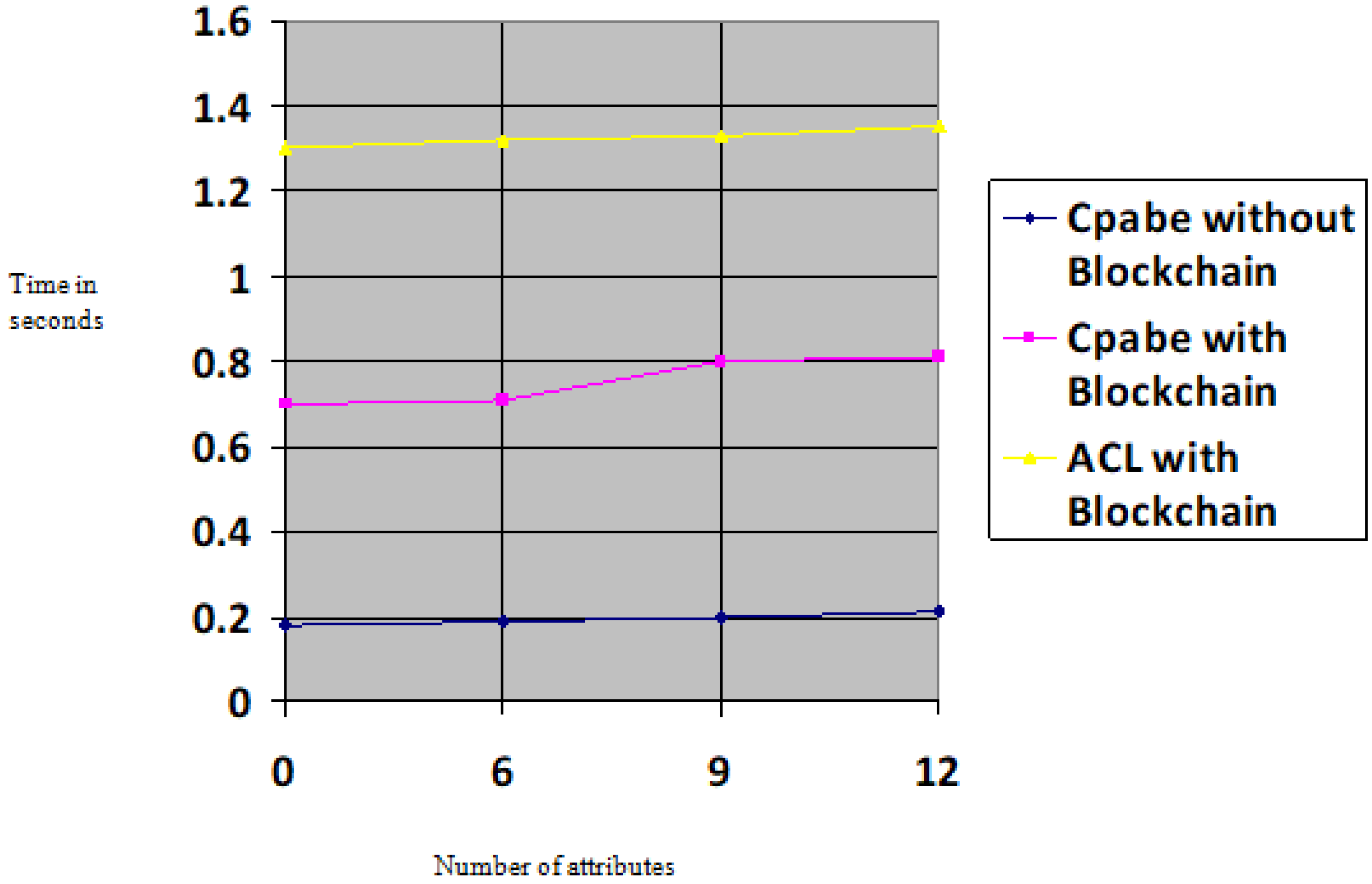
8. Performance Evaluation
8.1. An Attribute-Based Access Control Model for IoTs
8.2. Cost Evaluation and Comparison
9. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Tung, L. IoT Devices Will Outnumber the World’s Population This Year for the First Time; ZDNet, A RED VENTURES COMPANY; Volume 1. Available online: https://www.zdnet.com/article/iot-devices-will-outnumber-the-worlds-population-this-year-for-the-first-time/ (accessed on 7 February 2017).
- Top, G.I. Strategic IoT Technologies and Trends, Gartner. Available online: https://www.gartner.com/en/newsroom/press-releases/2018-11-07-gartner-identifies-top-10-strategic-iot-technologies-and-trends (accessed on 4 September 2019).
- Ekbatanifard, G. An Energy Efficient Data Dissemination Scheme for Distributed Storage in the Internet of Things. Comput. Knowl. Eng. 2018, 1, 1–8. [Google Scholar]
- Ahmad, I.; Shah, M.A.; Khattak, H.A.; Ameer, Z.; Khan, M.; Han, K. FIViz: Forensics Investigation through Visualization for Malware in Internet of Things. Sustainability 2020, 12, 7262. [Google Scholar] [CrossRef]
- Shrestha, A.; Vassileva, J. Towards decentralized data storage in general cloud platform for meta-products. In Proceedings of the International Conference on Big Data and Advanced Wireless Technologies, Blagoevgrad, Bulgaria, 10 November 2016; pp. 1–7. [Google Scholar]
- Meadows, A. To Share or Not to Share? That Is the (Research Data) Question. Available online: https://scholarlykitchen.sspnet.org/2014/11/11/to-share-or-not-to-share-that-is-the-research-data-question (accessed on 9 September 2021).
- Kiran, S.; Khattak, H.A.; Butt, H.I.; Ahmed, A. Towards Efficient Energy Monitoring Using IoT. In Proceedings of the 2018 IEEE 21st International Multi-Topic Conference (INMIC), Karachi, Pakistan, 1–2 November 2018; pp. 1–4. [Google Scholar]
- McMahan, B.; Ramage, D. Federated Learning: Collaborative Machine Learning without Centralized Training Data. Google AI Blog. Available online: https://ai.googleblog.com/2017/04/federated-learning-collaborative.html (accessed on 20 September 2021).
- Asghar, A.; Abbas, A.; Khattak, H.A.; Khan, S.U. Fog Based Architecture and Load Balancing Methodology for Health Monitoring Systems. IEEE Access 2021, 9, 96189–96200. [Google Scholar] [CrossRef]
- Andaloussi, Y.; Ouadghiri, M.; Maurel, Y.; Bonnin, J.; Chaoui, H. Access control in IoT environments: Feasible scenarios. Procedia Comput. Sci. 2018, 130, 1031–1036. [Google Scholar] [CrossRef]
- Deebak, B.D.; Al-Turjman, F.M. Privacy-preserving in smart contracts using blockchain and artificial intelligence for cyber risk measurements. J. Inf. Secur. Appl. 2021, 58, 102749. [Google Scholar]
- Gray, C. Storj vs. Dropbox: Why Decentralized Storage Is the Future. 2014. Available online: https://bitcoinmagazine.com/articles/storjvs-Dropboxdecentralized (accessed on 15 September 2021).
- Šarac, M.; Pavlović, N.; Bacanin, N.; Al-Turjman, F.; Adamović, S. Increasing privacy and security by integrating a Blockchain Secure Interface into an IoT Device Security Gateway Architecture. Energy Rep. 2021, 78, 1–8. [Google Scholar]
- Ripeanu, M. Peer-to-peer architecture case study: Gnutella network. In Proceedings of the First International Conference on Peer-to-Peer Computing, Linkoping, Sweden, 27–29 August 2001; pp. 99–100. [Google Scholar]
- Tseng, H.; Zhao, Q.; Zhou, Y.; Gahagan, M.; Swanson, S. Morpheus: Creating application objects efficiently for heterogeneous computing. ACM SIGARCH Comput. Archit. News 2016, 44, 53–65. [Google Scholar] [CrossRef]
- Giesler, M.; Pohlmann, M. The Anthropology of File Sharing: Consuming Napster as a Gift; Association for Consumer Research, University of Minnesota Duluth: Duluth, MN, USA, 2003; Volume 3. [Google Scholar]
- Good, N.; Krekelberg, A. Usability and privacy: A study of Kazaa P2P file-sharing. In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, Ft. Lauderdale, FL, USA, 5 April 2003; pp. 137–144. [Google Scholar]
- Pouwelse, J.; Garbacki, P.; Epema, D.; Sips, H. The bittorrent p2p file-sharing system: Measurements and analysis. In International Workshop on Peer-to-Peer Systems; Springer: Berlin/Heidelberg, Germany, 2005; pp. 205–216. [Google Scholar]
- Queiroz, M.; Telles, R.; Bonilla, S. Blockchain and supply chain management integration: A systematic review of the literature. Supply Chain Manag. Int. J. 2019, 25, 241–254. [Google Scholar] [CrossRef]
- Rehiman, K.; Veni, S. A trust management model for sensor enabled mobile devices in iot. In Proceedings of the 2017 International Conference on I-SMAC (IoT in Social; Analytics and Cloud), Palladam, India, 10–11 February 2017; pp. 807–810. [Google Scholar]
- Yuan, J.; Li, X. A reliable and lightweight trust computing mechanism for IoT edge devices based on multi-source feedback information fusion. IEEE Access 2018, 6, 23626–23638. [Google Scholar] [CrossRef]
- Shahid, H.; Shah, M.A.; Almogren, A.; Khattak, H.A.; Din, I.U.; Kumar, N.; Maple, C. Machine Learning-based Mist Computing Enabled Internet of Battlefield Things. ACM Trans. Internet Technol. (TOIT) 2021, 21, 1–26. [Google Scholar] [CrossRef]
- Ouaddah, A. A Blockchain Based Access Control Framework for the Security and Privacy of IoT with Strong Anonymity Unlinkability and Intractability Guarantees, 1st ed.; Elsevier Inc.: London, UK, 2018; Volume 115. [Google Scholar]
- Zhang, C.; Zhu, L.; Xu, C.; Sharif, K.; Du, X.; Guizani, M. LPTD: Achieving lightweight and privacy-preserving truth discovery in CIoT. Futur. Gener. Comput. Syst. 2019, 90, 175–184. [Google Scholar] [CrossRef] [Green Version]
- Atzori, L.; Iera, A.; Morabito, G. Siot: Giving a social structure to the internet of things. IEEE Commun. Lett. 2011, 15, 1193–1195. [Google Scholar] [CrossRef]
- Baldassarre, G.; Giudice, P.; Musarella, L.; Ursino, D. The MIoT paradigm: Main features and an ad-hoc crawler. Futur. Gener. Comput. Syst. 2019, 92, 29–42. [Google Scholar] [CrossRef]
- Baldassarre, G.; Giudice, P.; Musarella, L.; Ursino, D. A paradigm for the cooperation of objects belonging to different IoTs. In Proceedings of the 22nd International Database Engineering & Applications Symposium, Villa San Giovanni, Italy, 18 June 2018; pp. 157–164. [Google Scholar]
- Liu, J.; Xiao, Y.; Chen, C. Authentication and access control in the internet of things. In Proceedings of the 2012 32nd International Conference on Distributed Computing Systems Workshops, Macau, China, 18–21 June 2012; pp. 588–592. [Google Scholar]
- Aloqaily, M.; Otoum, S.; Ridhawi, I.; Jararweh, Y. An intrusion detection system for connected vehicles in smart cities. Ad. Hoc. Netw. 2019, 90, 101842. [Google Scholar] [CrossRef]
- Otoum, S.; Kantarci, B.; Mouftah, H. On the feasibility of deep learning in sensor network intrusion detection. IEEE Netw. Lett. 2019, 1, 68–71. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Zahmatkesh, H.; Shahroze, R. An overview of security and privacy in smart cities’ IoT communications. Trans. Emerg. Telecommun. Technol. 2019, 1, e3677. [Google Scholar] [CrossRef]
- Nawaz, A.; Ahmed, S.; Khattak, H.A.; Akre, V.; Rajan, A.; Khan, Z.A. Latest Advances in Interent Of Things and Big Data with Requirments and Taxonomy. In Proceedings of the 2020 Seventh International Conference on Information Technology Trends (ITT), Abu Dhabi, United Arab Emirates, 25–26 November 2020; pp. 13–19. [Google Scholar]
- Henna, S.; Davy, A.; Khattak, H.A.; Minhas, A.A. An Internet of Things (IoT)-Based Coverage Monitoring for Mission Critical Regions. In Proceedings of the 2019 10th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Canary Islands, Spain, 24–26 June 2019; pp. 1–5. [Google Scholar]
- Tewari, A.; Gupta, B. Security, privacy and trust of different layers in Internet-of-Things (IoTs) framework. Futur. Gener. Comput. Syst. 2020, 108, 909–920. [Google Scholar] [CrossRef]
- Rault, T.; Bouabdallah, A.; Challal, Y. Energy efficiency in wireless sensor networks: A top-down survey. Comput. Netw. 2014, 67, 104–122. [Google Scholar] [CrossRef] [Green Version]
- Islam, S.; Kwak, D.; Kabir, M.; Hossain, M.; Kwak, K. The internet of things for health care: A comprehensive survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Lee, I.; Lee, K. The Internet of Things (IoT): Applications, investments, and challenges for enterprises. Bus. Horiz. 2015, 58, 431–440. [Google Scholar] [CrossRef]
- Zhang, Z.K.; Cho, M.; Wang, C.W.; Hsu, C.W.; Chen, C.K.; Shieh, S. IoT security: Ongoing challenges and research opportunities. In Proceedings of the 2014 IEEE 7th International Conference on Service-Oriented Computing and Applications, Matsue, Japan, 17–19 November 2014; pp. 230–234. [Google Scholar]
- Baccelli, E.; Hahm, O.; Günes, M.; Wählisch, M.; Schmidt, T. RIOT OS: Towards an OS for the Internet of Things. In Proceedings of the 2013 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Turin, Italy, 14–19 April 2013; pp. 79–80. [Google Scholar]
- Dunkels, A.; Gronvall, B.; Voigt, T. Contiki-a lightweight and flexible operating system for tiny networked sensors. In Proceedings of the 29th Annual IEEE International Conference on Local Computer Networks, Tampa, FL, USA, 16–18 November 2004; pp. 455–462. [Google Scholar]
- Alromaihi, S.; Elmedany, W.; Balakrishna, C. Cyber security challenges of deploying IoT in smart cities for healthcare applications. In Proceedings of the 2018 6th International Conference on Future Internet of Things and Cloud Workshops (FiCloudW), Barcelona, Spain, 6–8 August 2018; pp. 140–145. [Google Scholar]
- Alsaadi, E.; Tubaishat, A. Internet of things: Features, challenges, and vulnerabilities. Int. J. Adv. Comput. Sci. Inf. Technol. 2015, 4, 1–13. [Google Scholar]
- Abomhara, M.; Køien, G.M. Security and privacy in the Internet of Things: Current status and open issues. In Proceedings of the 2014 International Conference on Privacy and Security in Mobile Systems (PRISMS), Aalborg, Denmark, 11–14 May 2014; pp. 1–8. [Google Scholar]
- Al-Turjman, F.; Baali, I. Machine learning for wearable IoT-based applications: A survey. In Transactions on Emerging Telecommunications Technologies; Bernabe, J., Hernández, J., Moreno, M., Gomez, A., Eds.; Willey: Hoboken, NJ, USA, 2019. [Google Scholar]
- Roman, R.; Zhou, J.; Lopez, J. On the features and challenges of security and privacy in distributed internet of things. Comput. Netw. 2013, 57, 2266–2279. [Google Scholar] [CrossRef]
- Cirani, S. A scalable and self-configuring architecture for service discovery in the internet of things. IEEE Internet Things J. 2014, 1, 508–521. [Google Scholar] [CrossRef]
- Tsai, C.W.; Lai, C.F.; Vasilakos, A. Future internet of things: Open issues and challenges. Wirel. Netw. 2014, 20, 2201–2217. [Google Scholar] [CrossRef]
- Antonakakis, M.; April, T.; Bailey, M.; Bernhard, M.; Bursztein, E.; Cochran, J.; Durumeric, Z.; Halderman, J.A.; Invernizzi, L.; Kallitsis, M.; et al. Understanding the mirai botnet. In Proceedings of the 26th {USENIX} Security Symposium ({USENIX} Security 17), Vancouver, BC, Canada, 16–18 August 2017; pp. 1093–1110. [Google Scholar]
- Khattak, H.A.; Tehreem, K.; Almogren, A.; Ameer, Z.; Din, I.U.; Adnan, M. Dynamic pricing in industrial internet of things: Blockchain application for energy management in smart cities. J. Inf. Secur. Appl. 2020, 55, 102615. [Google Scholar] [CrossRef]
- Kan, L.; Wei, Y.; Muhammad, A.; Siyuan, W.; Linchao, G.; Kai, H. A multiple blockchains architecture on inter-blockchain communication. In Proceedings of the 2018 IEEE International Conference on Software Quality, Reliability and Security Companion (QRS-C), Lisbon, Portugal, 16–20 July 2018; pp. 139–145. [Google Scholar]
- Lee, W.M. Using the metamask chrome extension. In Beginning Ethereum Smart Contracts Programming; Apress: Berkeley, CA, USA, 2019; pp. 93–126. [Google Scholar]
- Taş, R.; Tanrıöver, Ö.Ö. Building a decentralized application on the Ethereum blockchain. In Proceedings of the 2019 3rd International Symposium on Multidisciplinary Studies and Innovative Technologies (ISMSIT), Ankara, Turkey, 11–13 October 2019; pp. 1–4. [Google Scholar]
- Benet, J. Ipfs-content addressed, versioned, p2p file system. arXiv 2014, arXiv:1407.3561. [Google Scholar]
- Zichichi, M.; Ferretti, S.; D’Angelo, G. A distributed ledger based infrastructure for smart transportation system and social good. In Proceedings of the 2020 IEEE 17th Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 10–13 January 2020; pp. 1–6. [Google Scholar]
- Li, R.; Song, T.; Mei, B.; Li, H.; Cheng, X.; Sun, L. Blockchain for Large-Scale Internet of Things Data Storage and Protection. IEEE Trans. Serv. Comput. 2019, 12, 762–771. [Google Scholar] [CrossRef]
- Wang, S.; Zhang, Y.; Zhang, Y. A blockchain-based framework for data sharing with fine-grained access control in decentralized storage systems. IEEE Access 2018, 6, 38437–38450. [Google Scholar] [CrossRef]
- Ding, S.; Cao, J.; Li, C.; Fan, K.; Li, H. A Novel Attribute-Based Access Control Scheme Using Blockchain for IoT. IEEE Access 2019, 7, 38431–38441. [Google Scholar] [CrossRef]
- Wang, H.; He, D.; Shen, J.; Zheng, Z.; Zhao, C.; Zhao, M. Verifiable outsourced ciphertext-policy attribute-based encryption in cloud computing. Soft Comput. 2017, 21, 7325–7335. [Google Scholar] [CrossRef]
- Fernández, F.; Alonso, A.; Marco, L.; Salvachúa, J. A model to enable application-scoped access control as a service for IoT using OAuth 2.0. In Proceedings of the 2017 20th Conference on Innovations in Clouds, Internet and Networks (ICIN), Paris, France, 7–9 March 2017; pp. 322–324. [Google Scholar]
- Hummen, R.; Shafagh, H.; Raza, S.; Voig, T.; Wehrle, K. Delegation-based Authentication and Authorization for the IP-based Internet of Things. In Proceedings of the 2014 Eleventh Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), Singapore, 30 June–3 July 2014; pp. 284–292. [Google Scholar]
- Gusmeroli, S.; Piccione, S.; Rotondi, D. A capability-based security approach to manage access control in the internet of things. Math. Comput. Model 2013, 58, 1189–1205. [Google Scholar] [CrossRef]
- Biswas, K.; Muthukkumarasamy, V. Securing smart cities using blockchain technology. In Proceedings of the 2016 IEEE 18th international conference on high performance computing and communications; IEEE 14th international conference on smart city; IEEE 2nd international conference on data science and systems (HPCC/SmartCity/DSS), Sydney, NSW, Australia, 12–14 December 2016; pp. 1392–1393. [Google Scholar]
- Rehan, M.; Rehmani, M. Blockchain-Enabled Fog and Edge Computing: Concepts, Architectures and Applications: Concepts, Architectures and Applications; CRC Press: Boca Raton, FL, USA, 2020. [Google Scholar]
- Yu, K.P.; Tan, L.; Aloqaily, M.; Yang, H.; Jararweh, Y. Blockchain-enhanced data sharing with traceable and direct revocation in IIoT. IEEE Trans. Ind. Inform. 2021, 17, 7669–7678. [Google Scholar] [CrossRef]
- Šimunić, S. Upotreba Blockchain Tehnologije za Registraciju i Upravljanje IoT Uređajima; Department of Computer, Faculty of Engineering, University of Rijeka: Rijeka, Croatia, 2018. [Google Scholar]
- Do, H.; Ng, W. Blockchain-Based System for Secure Data Storage with Private Keyword Search. In Proceedings of the 2017 IEEE World Congress on Services (SERVICES), Honolulu, HI, USA, 25–30 June 2017. [Google Scholar]
- Zhang, G.; Li, T.; Li, Y.; Hui, P.; Jin, D. Blockchain-Based Data Sharing System for AI-Powered Network Operations. J. Commun. Inf. Netw. 2018, 3, 1–8. [Google Scholar] [CrossRef]
- Steichen, M.; Fiz, B.; Norvill, R.; Shbair, W.; State, R. Blockchain-Based, Decentralized Access Control for IPFS. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 1499–1506. [Google Scholar]
- Sifah, E. Chain-based big data access control infrastructure. J. Supercomput. 2018, 74, 4945–4964. [Google Scholar] [CrossRef]
- Zhang, Y.; Kasahara, S.; Shen, Y.; Jiang, X.; Wan, J. Smart contract-based access control for the internet of things. IEEE Internet Things J. 2019, 6, 1594–1605. [Google Scholar] [CrossRef] [Green Version]
- Nguyen, K.; Oualha, N.; Laurent, M. Securely outsourcing the ciphertext-policy attribute-based encryption. World Wide Web 2018, 21, 169–183. [Google Scholar] [CrossRef]
- Oualha, N.; Nguyen, K. Lightweight attribute-based encryption for the internet of things. In Proceedings of the 2016 25th International Conference on Computer Communication and Networks (ICCCN), Waikoloa, HI, USA, 1–4 August 2016; pp. 1–6. [Google Scholar]
- Hur, J.; Kang, K. Secure data retrieval for decentralized disruption-tolerant military networks. IEEE/ACM Trans. Netw. 2012, 22, 16–26. [Google Scholar] [CrossRef]
- Bethencourt, J.; Sahai, A.; Waters, B. Ciphertext-policy attribute-based encryption. In Proceedings of the 2007 IEEE Symposium on Security and Privacy (SP’07), Berkeley, CA, USA, 20–23 May 2007. [Google Scholar]
- Nishide, T.; Yoneyama, K.; Ohta, K. Attribute-based encryption with partially hidden encryptor-specified access structures. In Proceedings of the International Conference on Applied Cryptography and Network Security, New York, NY, USA, 3–6 June 2008; pp. 111–129. [Google Scholar]
- Khan, F.; Li, H.; Zhang, L.; Shen, J. An expressive hidden access policy CP-ABE. In Proceedings of the 2017 IEEE Second International Conference on Data Science in Cyberspace (DSC), Shenzhen, China, 26–29 June 2017; pp. 178–186. [Google Scholar]
- Zhou, Z.; Huang, D.; Wang, Z. Efficient privacy-preserving ciphertext-policy attribute based-encryption and broadcast encryption. IEEE Trans. Comput. 2013, 64, 126–138. [Google Scholar] [CrossRef]
- Phuong, T.; Yang, G.; Susilo, W. Hidden ciphertext policy attribute-based encryption under standard assumptions. IEEE Trans. Inf. Forensics Secur. 2015, 11, 35–45. [Google Scholar] [CrossRef]
- Hammi, M.; Bellot, P.; Serhrouchni, A. BCTrust: A decentralized authentication blockchain-based mechanism. In Proceedings of the 2018 IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- Ganache. Trufflesuite. Ganache ONE CLICK BLOCKCHAIN SOLUTION. Available online: https://www.trufflesuite.com/ganache (accessed on 15 September 2021).








| Ref. | Technology Used | Contributions | Addressed Problems |
|---|---|---|---|
| [15] | IoT and blockchain | Blockchain-based simple mechanism for database | IoTs applications Database |
| [62] | IoT, smart contract, and blockchain | A blockchain, smart contract, and IoT combination is used for identifying solutions | Complex processes automation |
| [63] | Blockchain edge/fog computing | Edge/fog working relationship with blockchain | Blockchain-enabled fog applications |
| [64] | IoT and blockchain | In IIOT, traceability and revocability with a blockchain-based access control system | Malicious users tracking and revocation |
| [65] | IoT, smart contract, and blockchain | Web interface for controlling entities information with smart contracts | Identity, interoperability, and security of IoT |
| Ref. | Author | Description of Research | Techniques | Contributions | Evaluation Criteria | Limitations |
|---|---|---|---|---|---|---|
| [55] | Li et al. 2018 | Blockchain for large-scale IoT data storage and protection | Distributed Hash Tables (DHTs) and edge computing | Security, accountability, and traceability | Transaction verificatio and distributed data storage | User authentication not provided; Will not work on a complicated access control scheme |
| [56] | Wang et al. 2018 | Blockchain-based fine-grained decentralized storage scheme | IPFS, Ethereum, and attribute-based encryption (ABE) technologies | Secure access control policies achieved; keyword search function; wrong results in the traditional cloud storage is solved | IoTs authentication and attribute-based AC | Attribute revocation is not considered |
| [57] | Ding et al. 2019 | Blockchain-based access control scheme | Elliptic curve digital signature algorithm and AKA protocol | Scalability, robustness, IoTs consensus independence, low computation, and communication overhead | Security authentication in the decentralized AC | No real-time scenario is considered |
| [66] | Do et al. 2017 | Blockchain-based private keyword searching scheme | Proof of storage and distributed encrypted data storage | Data integrity and enforcing proof-of-retrievability | Anonymous access control and off-chain | Outsourcing data storage; does not support credential revocation; Boolean keywords |
| [67] | Zhang et al. 2018 | Blockchain/cloud-based data storage scheme | Cloud and hyper ledger fabric | identity management, fine-grained access control, scalability, and distant access | Data chain and behavior chain permission levels | Single-system restriction and authentication |
| [68] | Steichen et al. 2018 | Blockchain-based decentralized access control for IPFS | Smart contract, IPFS, and Ethereum | Sharing of large sensitive files | Fixed gas amount | Authentication of nodes; more time-consuming |
| [69] | Sifah et al. 2018 | Chain-based big data access control infrastructure | ECDSA and PoC | Off-chain sovereign blockchain | security and data mismanagement and execution time | Inefficient in industries |
| [70] | Zhang et al. 2018 | Smart-contract-based access control for IoT | Ethereum smart contract platform | distributed and trustworthy access control for IoT systems | Gas price and timing | Overhead and capital cost |
| Ref. No | Blockchain | Scalability | Adaptability | Cost-Effective | Privacy Efficiency | Access Period |
|---|---|---|---|---|---|---|
| [79] | * | x | * | * | * | x |
| [70] | * | x | * | * | * | x |
| [71] | * | * | * | x | x | * |
| [55] | * | x | x | * | x | x |
| our model | * | * | * | * | * | * |
| Subject Attributes | Object Attributes |
|---|---|
| Name: | Name: |
| Dept: | Dept: |
| Org: | Org: |
| Role: | Place: |
| Others: | Others: |
| Subject Attributes | Object Attributes | Actions |
|---|---|---|
| Name: | Name: | Read:True |
| Dept=IS: | Dept=IS: | Write:False |
| Org:COMSATS: | Org:COMSATS | Execute:False |
| Role: | Place: | |
| Others: | Others: |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zaidi, S.Y.A.; Shah, M.A.; Khattak, H.A.; Maple, C.; Rauf, H.T.; El-Sherbeeny, A.M.; El-Meligy, M.A. An Attribute-Based Access Control for IoT Using Blockchain and Smart Contracts. Sustainability 2021, 13, 10556. https://0-doi-org.brum.beds.ac.uk/10.3390/su131910556
Zaidi SYA, Shah MA, Khattak HA, Maple C, Rauf HT, El-Sherbeeny AM, El-Meligy MA. An Attribute-Based Access Control for IoT Using Blockchain and Smart Contracts. Sustainability. 2021; 13(19):10556. https://0-doi-org.brum.beds.ac.uk/10.3390/su131910556
Chicago/Turabian StyleZaidi, Syed Yawar Abbas, Munam Ali Shah, Hasan Ali Khattak, Carsten Maple, Hafiz Tayyab Rauf, Ahmed M. El-Sherbeeny, and Mohammed A. El-Meligy. 2021. "An Attribute-Based Access Control for IoT Using Blockchain and Smart Contracts" Sustainability 13, no. 19: 10556. https://0-doi-org.brum.beds.ac.uk/10.3390/su131910556